About Us
DISCRYPT (DIStributed CRYptography and Privacy Technologies) is a research group from Universitat Autònoma de Barcelona dedicated to the study of decentralized systems, privacy-enhancing technologies, and applied cryptography. Its work focuses on developing secure and privacy-preserving solutions in areas such as blockchain, peer-to-peer networks, anonymous communication, and federated learning. We combine theoretical foundations with practical implementations to advance security and privacy in distributed technologies.
Our expertise
Blogs
Quotes
This (CBDB) has to be applied at a global level because, if there is an escape, that escape will be used
Christine Lagarde
ECB PresidentBitcoin is like anything else in the world: it's worth what people are willing to pay for it.
Stanley Druckenmiller
ResearcherLike the Internet, Bitcoin will change the way people interact and do business around the world.
Erik Voorhees
ResearcherBitcoin is very ideologically fulfilling, it's my form of political activism, but it's also a huge business opportunity.
Erik Voorhees
ResearcherLatest News
(17-21 Mar 2026) Discrypt at RECSI 2026
A delegation from Discrypt participated in Reunión Española sobre Criptología y Seguridad de la Información 2026 (RECSI 2026), held in Tenerife. RECSI is the leading scientific conference in Spain in the fields of cryptology and information security. This biennial meeting has played a central role in fostering the development of research and collaboration within the Spanish cryptographic community.
This year, Discrypt was strongly represented, with several members attending and presenting their latest research results across a wide range of topics, from privacy in machine learning to blockchain security.
Privacy Risks in Federated Learning
The conference opened with a presentation by Gorka Pineda (together with Antonina Serebriakova from UOC), who explored the impact of aggregation algorithms on property inference attacks in federated learning. Federated learning allows multiple participants to collaboratively train a shared model without directly exchanging their raw data, thereby reducing data exposure and improving privacy. However, privacy is not fully guaranteed: adversaries may still exploit the shared model updates to infer sensitive properties about participants’ local datasets.
This work focuses on how the choice of aggregation algorithm, one of the core components of federated learning, affects both the performance of the global model and its vulnerability to inference attacks. In particular, the study shows that aggregation strategies play a decisive role in shaping privacy risks. Notably, incorporating a proximal term, as done in the FedProx algorithm, can improve resistance to such attacks without sacrificing classification accuracy. That said, Gorka warned that the conclusions are drawn from experiments on a single dataset and exhibit some variability, highlighting the need for further validation.
Incentivizing the Discovery of Quantum Capabilities
In another talk, Roger Sala presented a novel approach to detecting the existence of a Cryptographically Relevant Quantum Computer (CRQC). Quantum computing poses a major threat to widely used cryptographic schemes such as RSA and elliptic-curve cryptography, which would become vulnerable in the presence of sufficiently powerful quantum adversaries. Despite significant progress in the field, it remains unclear when such capabilities will be achieved.
To address this uncertainty, Roger's work proposes leveraging economic incentives through Bitcoin. The idea is to deploy cryptographic honeypots (or canaries) on the Bitcoin network: specially crafted challenges whose solutions would only be feasible with quantum capabilities capable of breaking the Elliptic Curve Discrete Logarithm Problem. Successfully solving such challenges would publicly signal the existence of a CRQC, providing a transparent and economically motivated monitoring mechanism.
Towards Useful Proof-of-Work Mechanisms
Ghazaleh Keshavarzkalhori and Biel Castellarnau introduced a new perspective on proof-of-work (PoW) systems, a fundamental building block of blockchain technologies. Traditional PoW schemes rely on hash-based puzzles that, while effective for achieving distributed consensus, produce no intrinsic value beyond maintaining the network. This work revisits the essential properties required of PoW mechanisms and proposes an alternative approach based on the Elliptic Curve Discrete Logarithm Problem (ECDLP), a well-established hard problem in cryptography.
Ghazaleh and Biel analyze the computational complexity of their proposal and compare it with conventional hash-based approaches. Their results demonstrate that it is feasible to design secure PoW schemes grounded in meaningful mathematical problems, opening the door to "more useful" work in blockchain systems while preserving security and consensus guarantees.
Fingerprinting Hardware Wallets
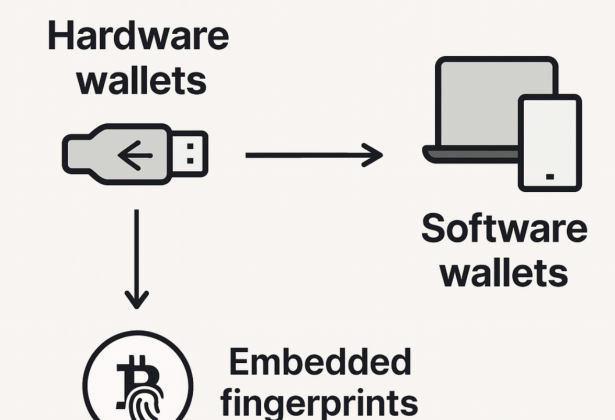
In his presentation, Domènec Madrid examined whether hardware wallets can be fingerprinted through their signature generation processes.
Hardware wallets are widely used to securely store cryptographic keys and sign transactions. This work dissects the internal steps involved in generating digital signatures and identifies which components are handled by the hardware device itself. The talk further explores whether subtle variations in the resulting signatures could act as identifiable signals, potentially enabling user fingerprinting. This line of research raises important questions about privacy and anonymity in cryptocurrency usage.
Modeling the Lightning Network
Finally, Yasser Hayali presented a comparative study of random graph models for the Lightning Network. The Lightning Network is a second-layer protocol built on top of Bitcoin that enables fast and scalable payments. Its behavior critically depends on the structure of its underlying payment-channel graph, making accurate modeling essential for evaluating routing strategies, protocol upgrades, and potential attacks.
Yasser's work compares several well-known random graph models (including Erdős-Rényi, Barabási-Albert, Watts-Strogatz, and a dynamic disassortative variant) against real-world data from the Lightning Network. The analysis considers metrics such as path lengths, clustering, assortativity, and network centrality. The results show that no single model fully captures the observed properties of the network. As a result, Yasser advocates for a hybrid model that combines multiple mechanisms, such as preferential attachment, disassortativity, and triadic closure, to better approximate the real topology.
Overall, RECSI 2026 provided an excellent platform for sharing ideas and networking with other researchers in cryptology and information security.
(14 Oct 2025) We attended the 7th International Conference on Blockchain Computing and Applications (BCCA 2025)
Discrypt group members presented their research at the 7th International Conference on Blockchain Computing and Applications (BCCA 2025), held in Dubrovnik, Croatia, from October 14-17, 2025. The presentations focused on enhancing Bitcoin Core performance through machine learning-based UTXO set management and analyzing security risks in Ethereum's non-custodial staking mechanisms.
(14 Oct 2025) BCCA 2025: A Risk Analysis of Non-custodial Staking in Ethereum
(25 Sep 2025) We organized the 9th International Workshop on Cryptocurrencies and Blockchain Technology (CBT)
(25 Sep 2025) We organized the 20th International Workshop on Data Privacy Management (DPM)
(28-29 May 2025) We attended the Cibersec+ workshop in UdL, Lleida
Discrypt group members gave various talks at the Cibersec+ workshop held at the University of Lleida. The topics presented included wallet fingerprinting, Bitcoin auctions, hardware wallet attacks, Lightning Network testbeds, and secure solutions for fair federated learning.